[AWS] ECS: Blue Green 배포 구성 with Terraform
ECS로 서버를 구성하게 되면, 기본적으로는 rolling update로 배포를 하게 된다.
여기에는 조금 문제가 있다. 배포를 하고 구버전 노드가 내려가기 전까지는 구버전과 신버전 노드가 공존할 수 있다는 것이다.
이걸 해결하려면 blue-green 배포 전략을 사용해야 한다.
CodeDeploy를 사용하고 target group을 비롯한 몇가지 구성을 추가하면 이를 달성할 수 있다.
이런 구조다.
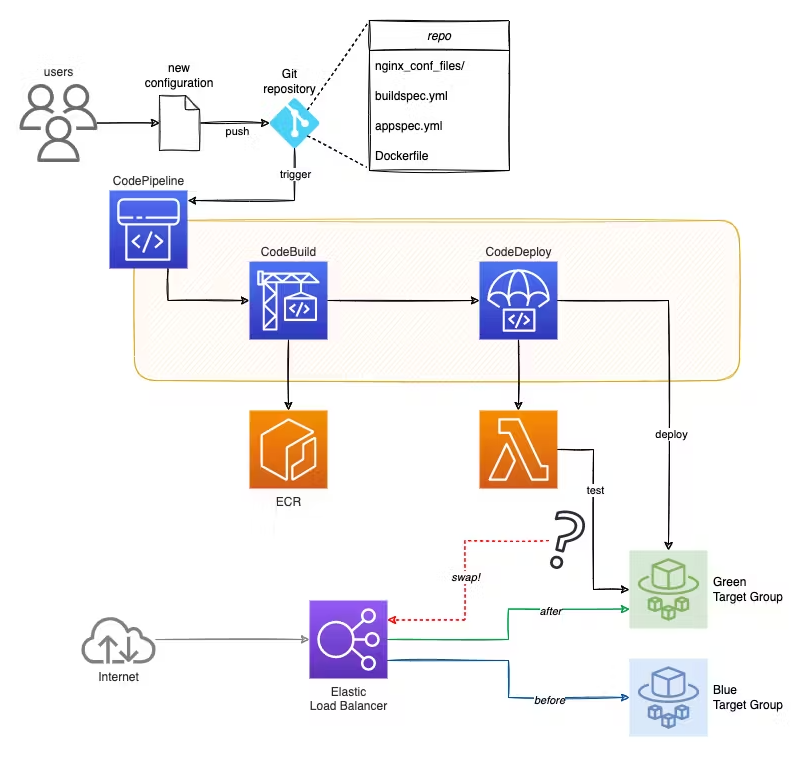 AWS에서는 target group을 이용해서 blue와 green을 구현한다.
AWS에서는 target group을 이용해서 blue와 green을 구현한다.
홀수번째 배포할때는 blue로 배포하고, 짝수번째 배포할때는 green으로 배포하면서, 로드밸런서 리스너만 때에 맞는 target group을 가리키게 스위칭하는 것이다.
여기서는 terraform을 이용해서 구성해보겠다.
전체 코드는 내 개인 레포지토리에 있다.
https://github.com/myyrakle/terraform/tree/master/aws/ecs-server/blue-green
먼저 타겟그룹을 2개 세팅해야 한다. rolling update에서는 하나면 충분했지만, 여기서는 2개가 필요하다.
동일하게 구성해주면 된다.
// 로드밸런싱에 사용할 대상 그룹
resource "aws_lb_target_group" "target_group_blue" {
name = "${local.resource_id}-blue"
port = var.target_group_port
protocol_version = var.target_group_protocol_version
protocol = var.target_group_protocol
vpc_id = var.vpc_id
target_type = "ip"
health_check {
enabled = true
path = var.healthcheck_uri
interval = var.healthcheck_interval
protocol = var.target_group_protocol
healthy_threshold = 5
unhealthy_threshold = 2
timeout = 20
}
tags = local.tags
}
// Blue Green 배포에 사용할 대상 그룹
resource "aws_lb_target_group" "target_group_green" {
name = "${local.resource_id}-green"
port = var.target_group_port
protocol_version = var.target_group_protocol_version
protocol = var.target_group_protocol
vpc_id = var.vpc_id
target_type = "ip"
health_check {
enabled = true
path = var.healthcheck_uri
interval = var.healthcheck_interval
protocol = var.target_group_protocol
healthy_threshold = 5
unhealthy_threshold = 2
timeout = 20
}
tags = local.tags
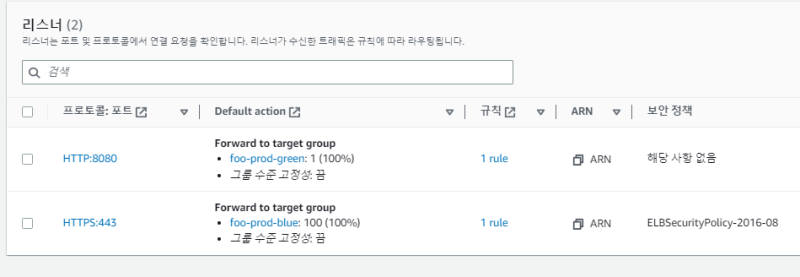
}그리고 리스너를 2개 설정해준다.
하나는 프로덕션 배포용, 하나는 테스트용이다.
// HTTP 리스너
resource "aws_lb_listener" "http_test_listener" {
load_balancer_arn = aws_lb.loadbalancer.arn
port = "8080"
protocol = "HTTP"
default_action {
type = "forward"
target_group_arn = aws_lb_target_group.target_group_green.arn
}
lifecycle {
ignore_changes = [default_action]
}
tags = local.tags
}
<br>
// HTTPS 리스너
resource "aws_lb_listener" "https_listener" {
load_balancer_arn = aws_lb.loadbalancer.arn
port = "443"
protocol = "HTTPS"
ssl_policy = "ELBSecurityPolicy-2016-08"
certificate_arn = var.certificate_arn
default_action {
type = "forward"
target_group_arn = aws_lb_target_group.target_group_blue.arn
}
lifecycle {
ignore_changes = [default_action]
}
tags = local.tags
}SSL을 적용하지 않을 거라면 443만 80으로 바꿔준다.
그리고 lifecycle을 이용해서 default_action을 처음 생성 이후에는 건들지 않도록 했다.
저기서 target_group_arn이 배포할때마다 계속 바뀔 것이기 때문이다.
다음은 리스너다.
// HTTP 리스너
// 트래픽 테스트
resource "aws_lb_listener" "http_test_listener" {
load_balancer_arn = aws_lb.loadbalancer.arn
port = "8080"
protocol = "HTTP"
default_action {
type = "forward"
target_group_arn = aws_lb_target_group.target_group_green.arn
}
lifecycle {
ignore_changes = [default_action]
}
tags = local.tags
}
<br>
// HTTPS 리스너
resource "aws_lb_listener" "https_listener" {
load_balancer_arn = aws_lb.loadbalancer.arn
port = "443"
protocol = "HTTPS"
ssl_policy = "ELBSecurityPolicy-2016-08"
certificate_arn = var.certificate_arn
default_action {
type = "forward"
target_group_arn = aws_lb_target_group.target_group_blue.arn
}
lifecycle {
ignore_changes = [default_action]
}
tags = local.tags
}리스너에는 트래픽 테스트용 리스너 하나와 메인 리스너 하나를 뒀다.
저기서는 메인 리스너를 https 하나만 뒀는데, ssl을 쓰지 않을 거라면 http로 바꾸면 된다.
https와 http를 전부 리스닝하고 싶다면, 다음과 같이 리다이렉트용 리스너를 추가한다.
// HTTP 리스너
resource "aws_lb_listener" "http_listener" {
load_balancer_arn = aws_lb.loadbalancer.arn
port = "80"
protocol = "HTTP"
default_action {
type = "redirect"
redirect {
port = "443"
protocol = "HTTPS"
status_code = "HTTP_301"
}
}
tags = local.tags
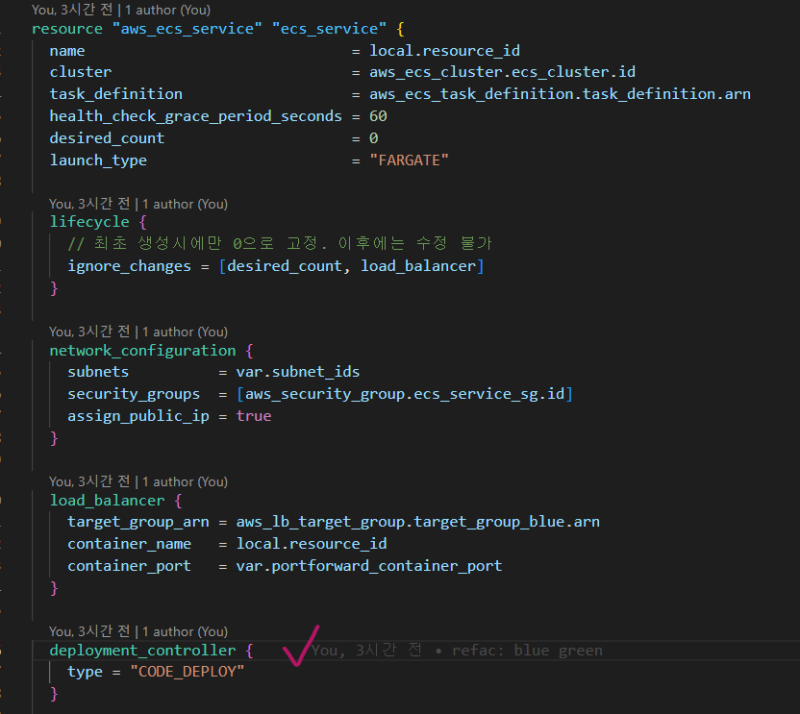
}그리고 서비스에도 설정을 추가해줘야 한다.
배포를 codedeploy에서 관리할 수 있도록 하래 구문을 삽입해준다.
deployment_controller {
type = "CODE_DEPLOY"
}
배포 정책을 결정할 deploy config를 하나 추가해주고
resource "aws_codedeploy_deployment_config" "config_deploy" {
deployment_config_name = local.resource_id
compute_platform = "ECS"
traffic_routing_config {
type = "AllAtOnce" // 한번에 교체
}
}deploy group을 정의한다.
이게 blue-green 배포를 주관할 녀석이다.
// blue-green 배포를 위한 code deploy group
resource "aws_codedeploy_deployment_group" "deployment_group" {
app_name = aws_codedeploy_app.deploy.name
deployment_config_name = aws_codedeploy_deployment_config.config_deploy.deployment_config_name
deployment_group_name = local.resource_id
service_role_arn = aws_iam_role.codedeploy_role.arn
// 실패시 롤백
auto_rollback_configuration {
enabled = true
events = ["DEPLOYMENT_FAILURE"]
}
blue_green_deployment_config {
deployment_ready_option {
action_on_timeout = "CONTINUE_DEPLOYMENT"
wait_time_in_minutes = 0
}
// green 배포 성공시 blue 인스턴스를 5분 후에 삭제합니다.
terminate_blue_instances_on_deployment_success {
action = "TERMINATE"
termination_wait_time_in_minutes = 5
}
}
deployment_style {
deployment_option = "WITH_TRAFFIC_CONTROL"
deployment_type = "BLUE_GREEN"
}
ecs_service {
cluster_name = aws_ecs_cluster.ecs_cluster.name
service_name = aws_ecs_service.ecs_service.name
}
load_balancer_info {
target_group_pair_info {
prod_traffic_route {
listener_arns = [aws_lb_listener.https_listener.arn]
}
test_traffic_route {
listener_arns = [aws_lb_listener.http_test_listener.arn]
}
target_group {
name = aws_lb_target_group.target_group_blue.name
}
target_group {
name = aws_lb_target_group.target_group_green.name
}
}
}
}저러면 prod_traffic_route와 test_traffic_route에 들어간 리스너를 자동으로 교체해준다.
그리고 codepipeline의 deploy 스텝을 수정한다.
stage {
name = "Deploy"
action {
name = "Deploy"
category = "Deploy"
owner = "AWS"
provider = "CodeDeployToECS"
input_artifacts = ["Build"]
version = "1"
run_order = 1
configuration = {
ApplicationName = aws_codedeploy_app.deploy.name
DeploymentGroupName = aws_codedeploy_deployment_group.deployment_group.deployment_group_name
TaskDefinitionTemplateArtifact = "Build"
TaskDefinitionTemplatePath = "taskdef.json"
AppSpecTemplateArtifact = "Build"
AppSpecTemplatePath = "appspec.json"
}
}
}provider를 ECS에서 CodeDeployToECS로 변경하고, configuration에 몇가지 설정이 추가됐다.
그래서 작업정의와 appspec을 이전 단계인 build에서 받아와야 하는데... 난 이걸 프로젝트 코드에 넣고 싶지 않았다.
그래서 terraform에 local 변수로 때려박고
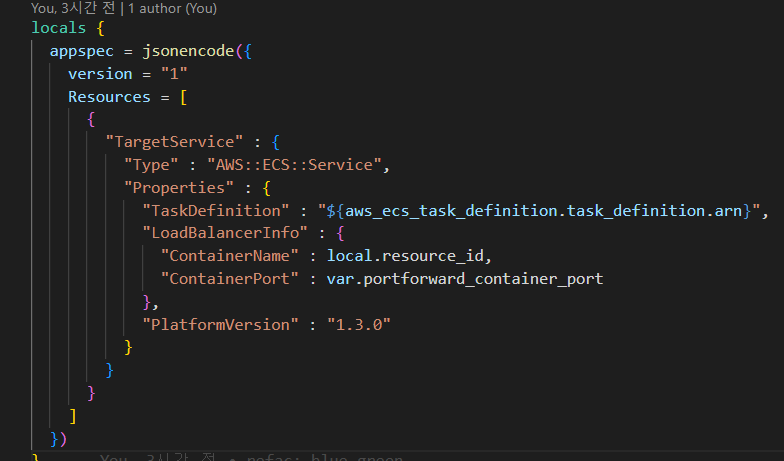
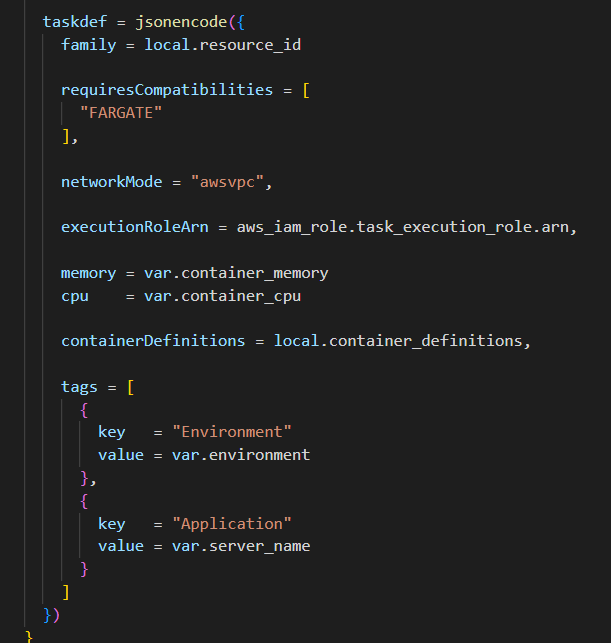
codebuild 환경변수에 넣어서
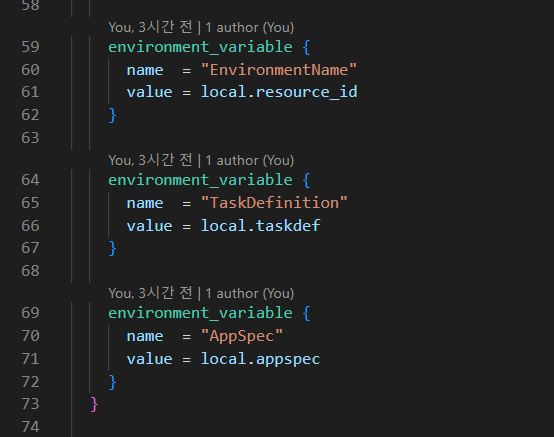
buildspec에서 emit해주게 했다.
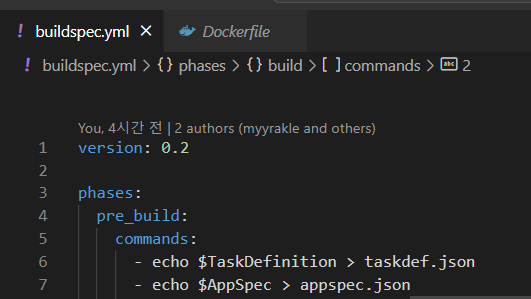 내가 사용한 buildspec 전체 코드다.
내가 사용한 buildspec 전체 코드다.
version: 0.2
phases:
pre_build:
commands:
- echo $TaskDefinition > taskdef.json
- echo $AppSpec > appspec.json
- printf '{"imageURI":"%s"}' "$AWS_ACCOUNT_ID.dkr.ecr.$AWS_DEFAULT_REGION.amazonaws.com/$IMAGE_REPO_NAME:$IMAGE_TAG" > imageDetail.json
- echo Logging in to Amazon ECR...
- aws ecr get-login-password --region $AWS_DEFAULT_REGION | docker login --username AWS --password-stdin $AWS_ACCOUNT_ID.dkr.ecr.$AWS_DEFAULT_REGION.amazonaws.com
build:
commands:
- echo Build started on `date`
- echo Building the Docker image...
- docker build -t $AWS_ACCOUNT_ID.dkr.ecr.$AWS_DEFAULT_REGION.amazonaws.com/$IMAGE_REPO_NAME:$IMAGE_TAG .
- docker tag $AWS_ACCOUNT_ID.dkr.ecr.$AWS_DEFAULT_REGION.amazonaws.com/$IMAGE_REPO_NAME:$IMAGE_TAG $AWS_ACCOUNT_ID.dkr.ecr.$AWS_DEFAULT_REGION.amazonaws.com/$IMAGE_REPO_NAME:$CODEBUILD_BUILD_NUMBER
post_build:
commands:
- echo Build completed on `date`
- echo Pushing the Docker image...
- docker push $AWS_ACCOUNT_ID.dkr.ecr.$AWS_DEFAULT_REGION.amazonaws.com/$IMAGE_REPO_NAME:$IMAGE_TAG
- docker push $AWS_ACCOUNT_ID.dkr.ecr.$AWS_DEFAULT_REGION.amazonaws.com/$IMAGE_REPO_NAME:$CODEBUILD_BUILD_NUMBER
artifacts:
files:
- 'appspec.json'
- 'taskdef.json'
- 'imageDetail.json'
secondary-artifacts:
DefinitionArtifact:
files:
- appspec.yaml
- taskdef.json
- imageDetail.jsonappspec의 경우에는 원한다면 hooks을 사용해서 더 많은 검증을 수행할 수 있다.
해서, 최초로 배포를 해서 로드밸런서에 도메인도 붙이면
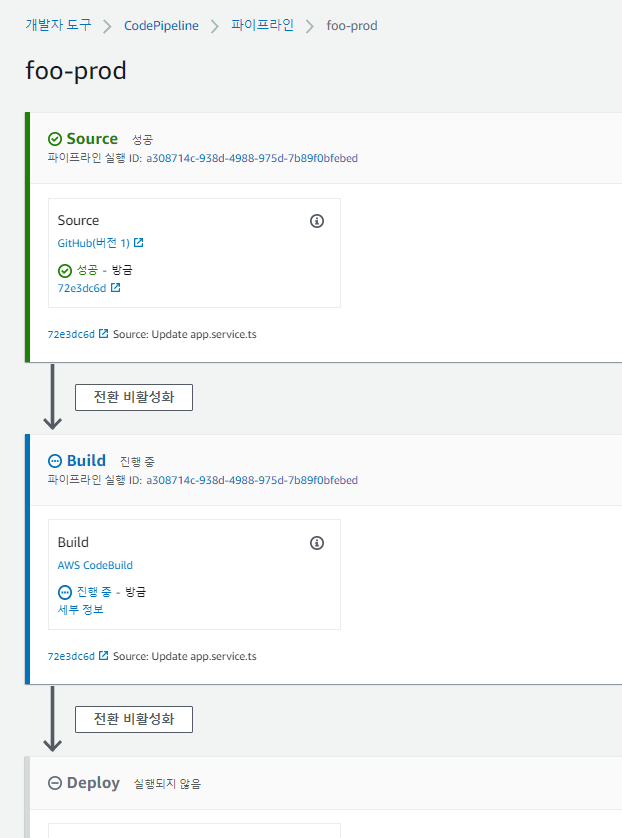
이렇게 잘 뜰 것이고
추가로 또 배포 트리거를 걸면
대상그룹도 자동으로 바뀌고
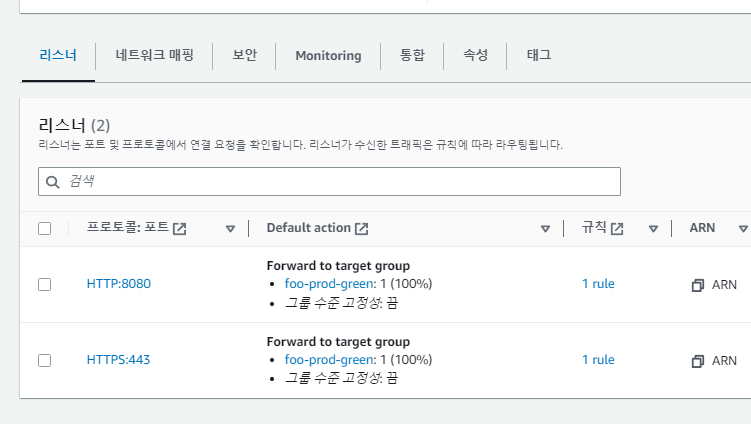
한번에 트래픽 전환하면서
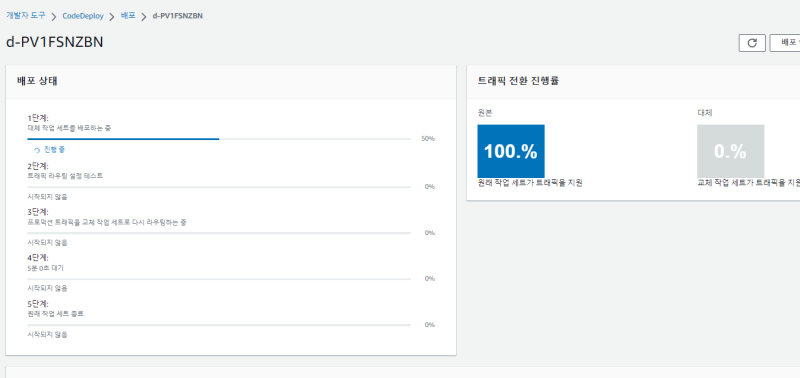
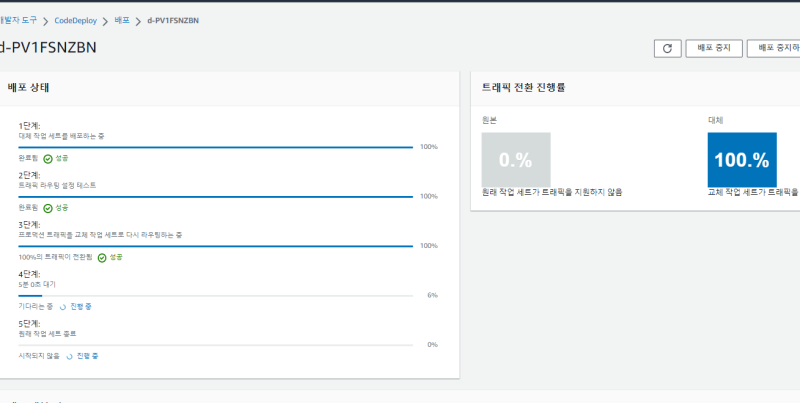
잘 바뀔 것이다.
이걸 잘 응용하면 carary 배포 같은 것도 구현할 수 있다.
참조
https://docs.aws.amazon.com/ko_kr/AmazonECS/latest/developerguide/create-blue-green.html
https://docs.aws.amazon.com/ko_kr/AWSCloudFormation/latest/UserGuide/blue-green.html
https://faun.pub/aws-ecs-blue-green-deployment-setup-using-terraform-b56bb4f656ea
https://letsmake.cloud/bluegreen-fargate
https://repost.aws/questions/QUGByFL5XzT26SA7lTCz3htQ/questions/QUGByFL5XzT26SA7lTCz3htQ/codepipeline-codedeploy-blue-green-ecs-insufficient-permissions?
https://arnav40.medium.com/deploy-nodejs-on-ecs-fargate-using-terraform-with-support-for-blue-geen-deployment-using-codedeploy-a750c6214153